Kash Patel Email Hacked: What It Means and What Small Businesses Should Learn
Disclosure: This article contains no affiliate links. It is purely informational.
On March 27, 2026, an Iran-linked hacking group called Handala published over 300 emails and personal photographs from what appears to be FBI Director Kash Patel’s personal Gmail account. The FBI confirmed the breach the same day, stating it had taken steps to mitigate risks and noting that the exposed material was historical in nature and involved no government information.
This is national security news. It is also a direct lesson for small business owners, because the technique that compromised the FBI director’s personal account is the same one hitting business owners’ inboxes every day.
What happened
Kash Patel email hacked: what the FBI confirmed
Handala, a pro-Iranian hacktivist group (hacktivists are hackers who carry out attacks for political or ideological reasons rather than financial gain), that the Justice Department has linked to Iran’s Ministry of Intelligence and Security, published the contents of what it said was Patel’s personal Gmail account. The dump included more than 300 emails and several photographs, with most of the emails dated between 2010 and 2019.
The FBI issued a statement confirming the breach: “The FBI is aware of malicious actors targeting Director Patel’s personal email information, and we have taken all necessary steps to mitigate potential risks associated with this activity. The information in question is historical in nature and involves no government information.”
TechCrunch confirmed that at least some of the leaked emails were authentic by verifying information in the message headers. Reuters reported it could not independently authenticate all published emails, though a Justice Department official said the breach was real and the material appeared authentic. NBC News similarly did not forensically verify all emails as authentic.
The attack appears to be retaliatory. On March 19, 2026, the Justice Department and FBI seized four domains tied to Handala’s operations, accusing the group of running hack-and-leak campaigns and psychological operations on behalf of Iranian intelligence. Handala responded directly: the published emails included a message stating the FBI “shouldn’t have started a confrontation with us.”
What was exposed
Personal data, not government secrets: and why that still matters
According to Axios, the leaked emails came exclusively from Patel’s personal Gmail account, not his official FBI inbox. The contents included travel receipts, family correspondence, tax-related emails, apartment rental inquiries from his time in Washington, D.C., and photographs from personal trips. NBC News reported that metadata indicated the files were organized into folders last modified in May 2025, suggesting the hack occurred earlier and the release was timed deliberately.
A cybersecurity researcher at Sublime Security told NBC News that Iranian actors often sit on hacked material and release it strategically: “Looks like something they had sitting around. Iranian actors sit on all kinds of odds and ends for a rainy day.”
The absence of government secrets does not make the exposure harmless. Personal email archives contain travel patterns, contact lists, financial details, relationship information, and years of correspondence that can be used for social engineering (manipulating people into revealing information by exploiting personal details or relationships), reputation attacks, and future targeting. The goal of hack-and-leak operations is often embarrassment and influence, not espionage.
The group behind it
Who is Handala?
Handala presents itself as a pro-Palestinian hacktivist collective, but Western security researchers and the Justice Department describe it as a persona used by Iranian government cyberintelligence units operating under the Ministry of Intelligence and Security. The group’s name comes from a character in the political cartoons of Palestinian artist Naji al-Ali.
Since US and Israeli military operations against Iran began in February 2026, Handala has been moving faster and hitting harder. Earlier in March 2026, TechCrunch and CNN reported that Handala claimed a destructive cyberattack against Stryker, a Michigan-based medical technology company. Stryker has not publicly confirmed the full extent of any damage. It has also published personal data of individuals linked to Israeli defense organizations and claimed breaches of other major companies.
Check Point’s chief of staff told Reuters that the hack-and-leak operation against Patel was part of Iran’s strategy to embarrass US officials and make them feel vulnerable, adding that the Iranians are “firing whatever they have.” The State Department is currently offering a reward of up to $10 million for information leading to identification of Handala members.
The business lesson
What the Kash Patel email hack means for your business
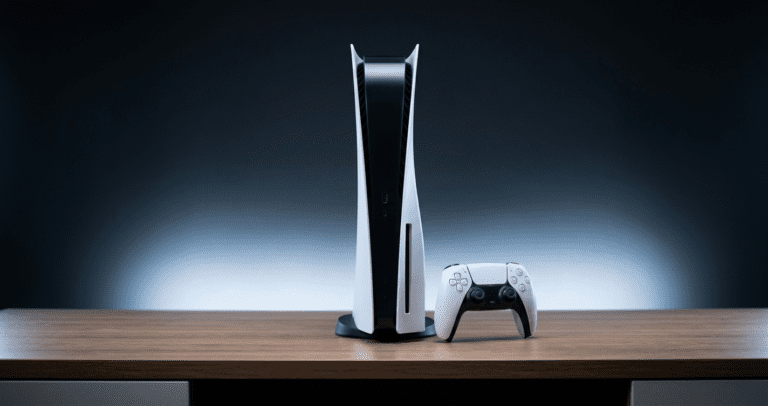
The FBI director’s personal Gmail account got compromised. Not a classified system. Not a government server with advanced security infrastructure. A personal Gmail account, the same platform millions of small business owners use every day for vendor emails, client correspondence, financial records, and sensitive communications.
A small business owner’s personal email account contains years of the same kind of material that made this breach newsworthy: travel records, financial documents, supplier contracts, employee information, and relationship history. The attacker targeting a small business is not a nation-state, but the technique is identical: find the weakest link, gain access, and use whatever is there. Attackers go where access is easiest and where the exposure is most useful. A personal account tied to a business owner is often the easiest path to business-relevant information.
Four practical steps this incident highlights:
1. Enable two-factor authentication on every email account, personal accounts included. The most common way personal Gmail accounts get compromised is through phishing or reused passwords. Two-factor authentication stops both attack vectors even when a password is exposed. For Gmail: go to myaccount.google.com, then Security, then 2-Step Verification, then Get started. Use an authenticator app rather than SMS if possible. SMS codes can be intercepted. Google Authenticator and Microsoft Authenticator are both free. Our guide to setting up two-step verification for your business walks through the full setup.
2. Stop reusing passwords. If the password on your personal Gmail is the same as any other account, a breach of any one of those accounts exposes all of them. A password manager (an app that generates and stores unique passwords for every account) eliminates this risk with minimal effort. Bitwarden is free and open source. 1Password costs $36 per year and is well-regarded for small business use. Either is better than a spreadsheet or recycled passwords.
3. Treat old accounts as active risks. The Patel emails appear to have been compromised before they were released. Old Gmail accounts, unused accounts from prior business setups, and accounts tied to domains you no longer use are all potential entry points. Review and lock down or close accounts you no longer actively manage. To find forgotten accounts: search your primary email inbox for the phrases “welcome to,” “verify your email,” and “confirm your account.” These phrases surface registration emails from old services. For each one, either log in and enable 2FA or use the account deletion option. In practice, a business owner who has operated for ten years typically has accounts tied to two or three prior domains, services they stopped using, and at least one account where the password is a variation of something they used everywhere years ago. Every one of those is a potential entry point.
4. Don’t assume “no business data” means “no risk.” The FBI’s statement that no government information was exposed did not end the story. A personal inbox contains enough context about a person’s life, contacts, and patterns to enable social engineering, relationship targeting, and reputation attacks. The same is true for a business owner’s personal account.
The threat level is different. The vulnerability is the same.
If you use Microsoft 365 and want to lock down admin access as a next step beyond personal account security, our guide to Microsoft Entra PIM covers the tools Microsoft provides for controlling who has privileged access to your business environment, and for how long.